Introduction
Both OnPremise Exchange server and Office 365 Exchange admin Center uses a large set of predefined permissions, those can be used to grant permissions to your administrators and users instantly. Here the permissions features are used to set up role-based permissions for your Exchange server new organization up and running quickly.
In Exchange Server, the permissions that you grant to administrators and users are based on management roles. A role defines the set of tasks that an administrator or user can perform. When a role is assigned to an administrator or user, that person is granted the permissions provided by the role. Roles give permissions to perform tasks to administrators and users by making cmdlets available to those who are assigned the roles.
Table of Contents
- Role groups and role assignment policies
- How to access Exchange Admin Center – Permissions
- Admin role
- Important role groups and Assigned roles
- End-User role
- Contact information
- Profile information
- Distribution groups
- Distribution group memberships
- Other roles
- Outlook WebApp Policies
- Administrative Units
- Conclusion
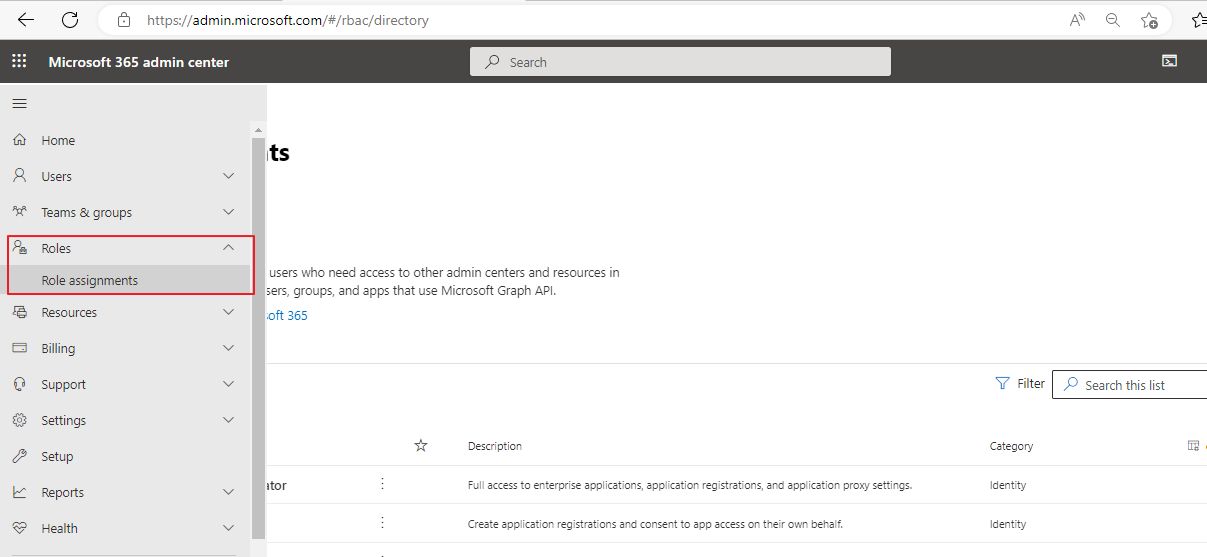
Now Office 365 admin center becomes Microsoft 365 admin center, and is tightly integrated with Azure AD, the role & role assignments are classified into two categories, and are grouped under two names Azure AD and Exchange separately in Roles → Role assignment section.
Within the conventional Exchange admin center, you’ll now find two distinct entities—the Classic Exchange admin center and the Microsoft 365 admin center. Under Roles, you have two sub-entities called Role Assignments and Administrative Units.
In this blog, we delve into two types of roles: Administrative roles and End-user roles. Additionally, we explore Role Groups and Role Assignment Policies, along with Outlook WebApp Policies. Discover the power of streamlined administration and configuration in the Exchange Administration Center.
- Administrative roles: These roles contain permissions that can be assigned to administrators or specialist users using role groups that manage a part of the Exchange organization, such as recipients, servers, or databases.
- End-user roles: These roles, assigned using role assignment policies, enable users to manage aspects of their own mailbox and distribution groups that they own. End-user roles begin with the prefix My.
Role groups and role assignment policies
- Roles grant permissions to perform tasks in Exchange Server, but you need an easy way to assign them to administrators and users. Exchange Server provides you with the following to help you do that:
- Role groups: Role groups enable you to grant permissions to administrators and specialist users.
Role assignment policies: Role assignment policies enable you to grant permission to end users to change settings on their own mailbox or distribution groups that they own.
How to access Exchange Admin Center – Permissions
Login to Microsoft 365 Admin Center with a Global administrator or an administrator privileged user using the below URL Home – Microsoft 365 admin center
Choose Role → Role assignments from the left main menu.
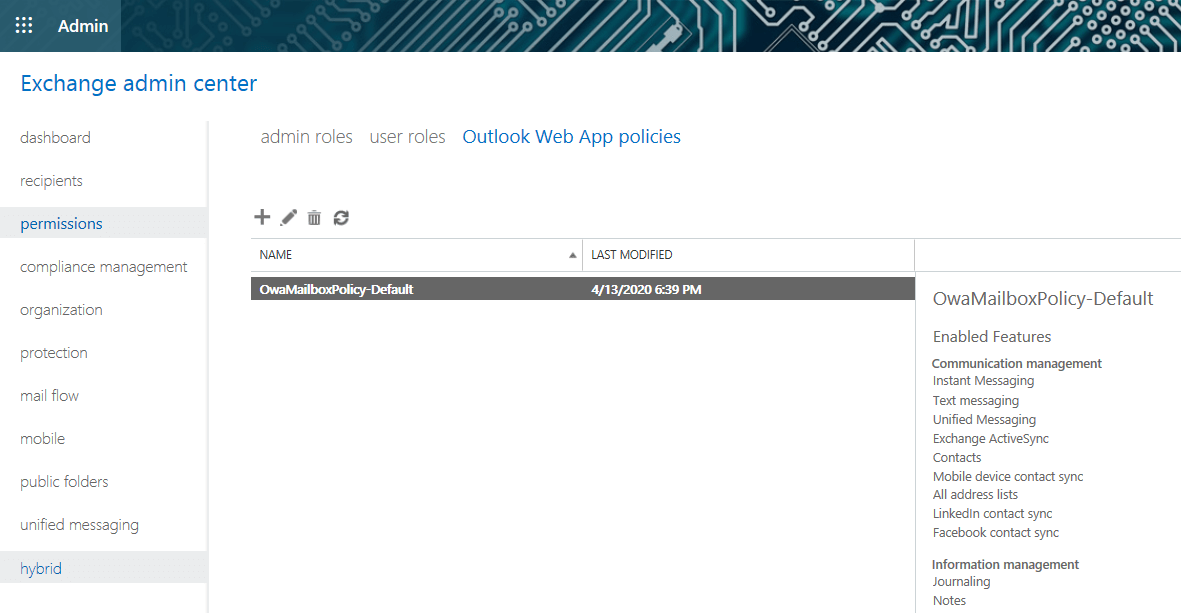
Exchange admin center – Permission constitutes three parts admin roles, user roles, and Outlook Web app policies.
Admin role
In the Admin role, you have 19 predefined role groups available for assigning roles to the administrators or specialized users. You can edit any of these 19 predefined role groups, can add roles & members on it. For example, Compliance Management is a role group, on editing you can add/remove roles from the group and can add/remove members from the group.
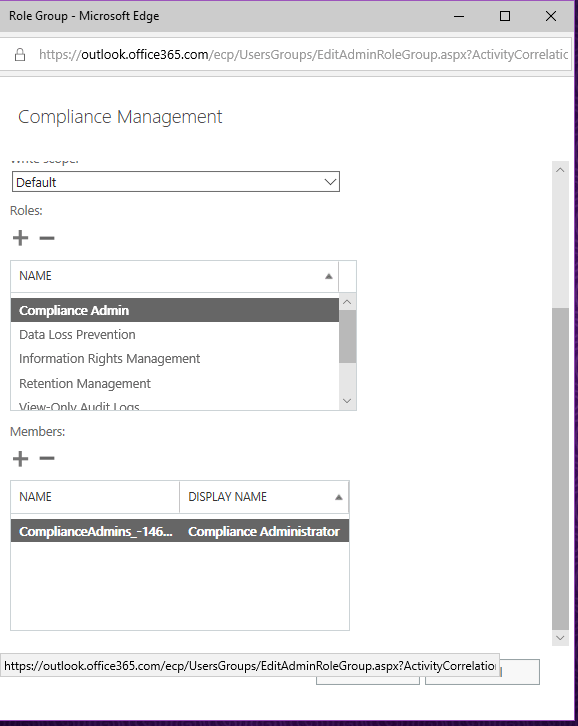
Important role groups and Assigned roles
By default, in Exchange server, you have prebuilt role groups and automatically assigned roles into it. Users can modify each role group and can add/remove roles & can add/remove members into it. Some of the role groups and assigned roles with their description given below.
Discovery Management – Members of this management role group can perform searches of mailboxes in the Exchange organization for data that meets specific criteria.
Assigned Roles – ApplicationImpersonation, Legal Hold, Mailbox Search
Help Desk – Members of this management role group can view and manage the configuration for individual recipients and view recipients in an Exchange organization. Members of this role group can only manage the configuration each user can manage on his or her own mailbox. Additional permissions can be added by assigning additional management roles to this role group.
Assigned Roles – Reset Password, User Options, View-Only Recipients
Hygiene Management – Members of this management role group can manage Exchange anti-spam features and grant permissions for antivirus products to integrate with Exchange.
Assigned Roles – Transport Hygiene, View-Only Configuration, View-Only Recipients
Organization Management – Members of this management role group have permissions to manage Exchange objects and their properties in the Exchange organization. Members can also delegate role groups and management roles in the organization. This role group shouldn’t be deleted.
Assigned Roles – ApplicationImpersonation, Audit Logs, Compliance Admin, Data Loss Prevention, Distribution Groups, E-Mail Address Policies, Federated Sharing, Information Rights Management, Journaling, Legal Hold, Mail Enabled Public Folders, Mail Recipient Creation, Mail Recipients, Mail Tips, Message Tracking, Migration, Move Mailboxes, Org Custom Apps, Org Marketplace Apps, Organization Client Access, Organization Configuration, Organization Transport Settings, Public Folders, Recipient Policies, Remote and Accepted Domains, Reset Password, Retention Management, Role Management, Security Admin, Security Group Creation, and Membership, Security Reader, Team Mailboxes, Transport Hygiene, Transport Rules, UM Mailboxes, UM Prompts, Unified Messaging, User Options, View-Only Audit Logs, View-Only Configuration, View-Only Recipients.
Recipient Management – Members of this management role group have the right to create, manage, and remove Exchange recipient objects in the Exchange organization.
Assigned Roles – Distribution Groups, Mail Recipient Creation, Mail Recipients, Message Tracking, Migration, Move Mailboxes, Recipient Policies, Reset Password, Team Mailboxes.
Records Management – Members of this management role group have permissions to manage and dispose of record content.
Assigned Roles – Audit Logs, Journaling, Message Tracking, Retention Management, Transport Rules
Security Administrator – Membership in this role group is synchronized across services and managed centrally. This role group is not manageable through the administrator portals. Members of this role group may include cross-service administrators, as well as external partner groups, and Microsoft Support. By default, this group may not be assigned any roles. However, it will be a member of the Security Administrators role groups and will inherit the capabilities of that role group.
Assigned Roles – Security Admin
End-User role
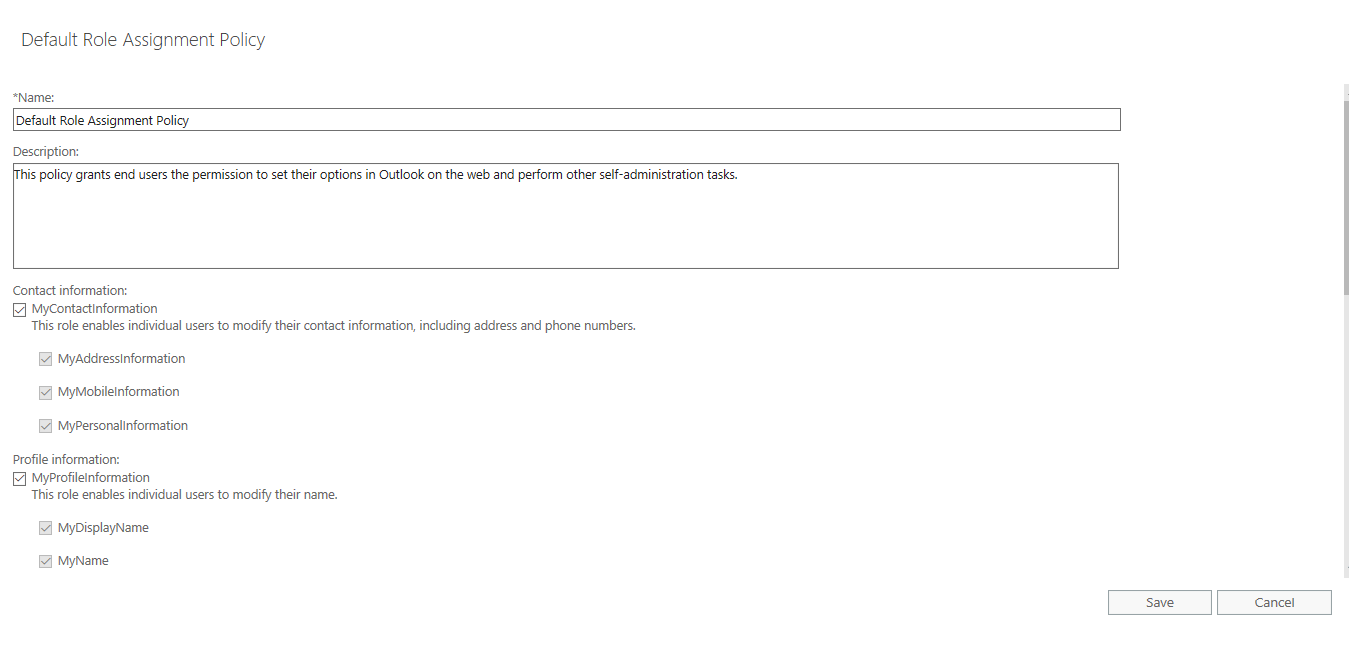
Always assigned to nonadministrator end-users using role assignment policies. By default End-user role has one Default Role Assignment Policy. This policy grants end-users permission to set their options in Outlook on the web and perform other self-administration tasks.
Usually this policy details the end user’s personal information, and settings related to his personal mailbox. All these user’s personal information and personal mailbox settings can be enabled or disabled by selecting/deselecting individual settings checkboxes. You can also customize these policies by creating a new policy and adopting the required policies selectively.
Contact information
MyContactInformation – This role enables individual users to modify their contact information, including the address and phone numbers.
Profile information
MyProfileInformation – This role enables individual users to modify their name.
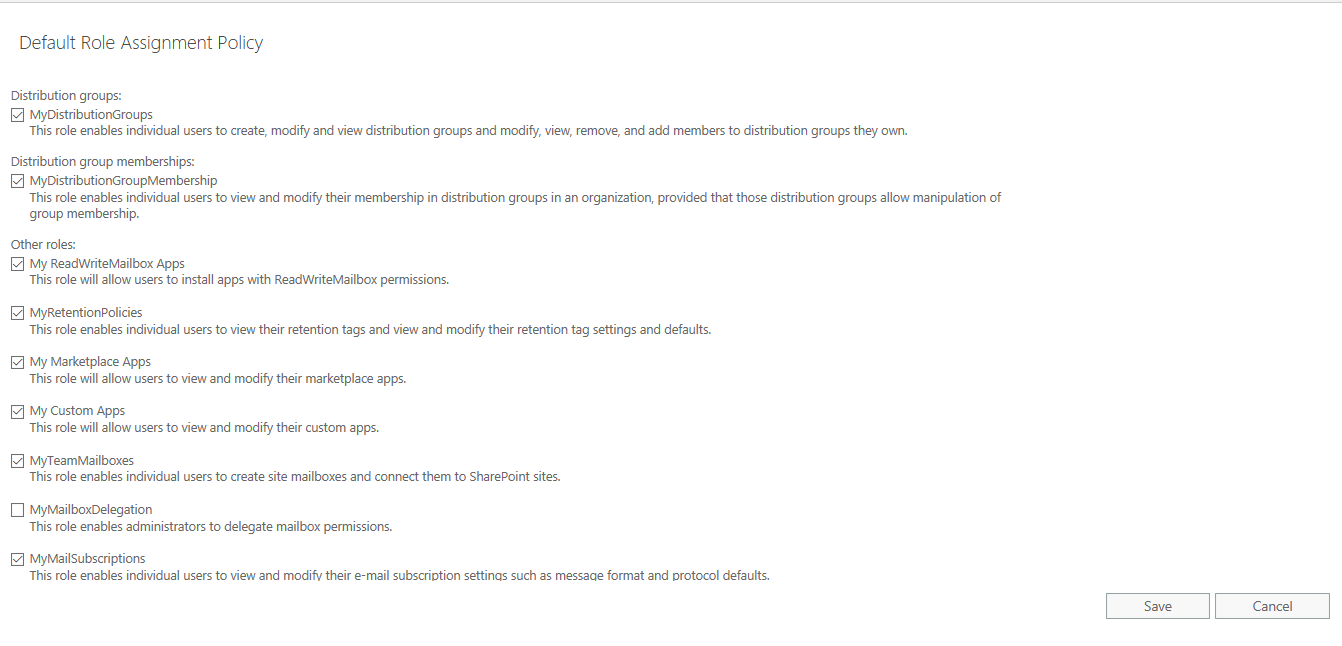
Distribution groups
MyDistributionGroups – This role enables individual users to create, modify and view distribution groups and modify, view, remove, and add members to distribution groups they own.
Distribution group memberships
MyDistributionGroupMembership – This role enables individual users to view and modify their membership in distribution groups in an organization, provided that those distribution groups allow manipulation of a group membership.
Other roles
My ReadWriteMailbox Apps – This role will allow users to install apps with ReadWriteMailbox permissions.
MyRetentionPolicies – This role enables individual users to view their retention tags and view and modify their retention tag settings and defaults.
My Marketplace Apps – This role will allow users to view and modify their marketplace apps.
My Custom Apps – This role will allow users to view and modify their custom apps.
MyTeamMailboxes – This role enables individual users to create site mailboxes and connect them to SharePoint sites.
MyMailSubscriptions – This role enables individual users to view and modify their e-mail subscription settings such as message format and protocol defaults.
MyVoiceMail – This role enables individual users to view and modify their voice mail settings.
MyBaseOptions – This role enables individual users to view and modify the basic configuration of their own mailbox and associated settings.
MyTextMessaging – This role enables individual users to create, view, and modify their text messaging settings.
Outlook WebApp Policies
These policies are exclusively for end users who access their mailboxes through Outlook Web Access (OWA), and this is based on the all & enabled features available in the OWA interface.
By default, here are the listed features are enabled under these categories
Communication Management – Instant Messaging, Text messaging, Unified Messaging, Exchange ActiveSync, Contacts, Mobile device contact sync, All address lists, LinkedIn contact sync, Facebook contact sync
Information management – Journaling, Notes, Inbox Rules, Recover deleted items
User experience – Themes, Premium client, Email signature, Places, Weather, Interesting calendars
Time management – Calendar, Tasks, Reminders, and notifications
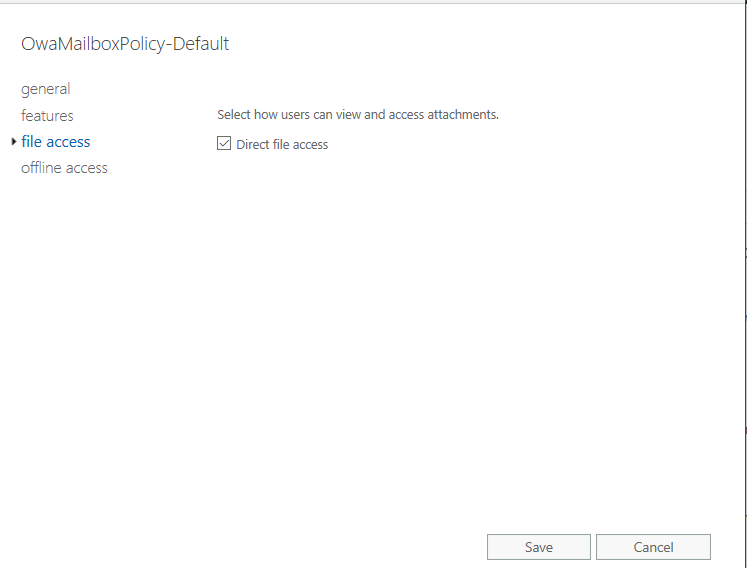
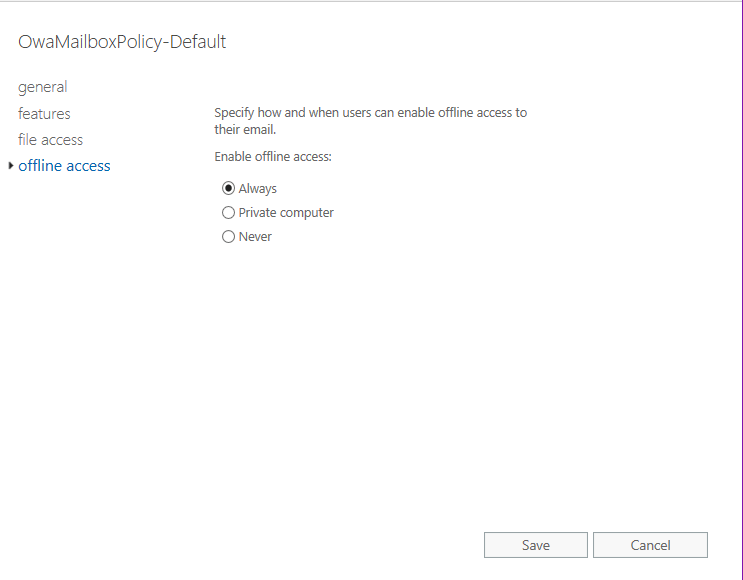
You can also edit the default OwaMailboxPolicy and change the other settings, such as file access and offline access settings.
File access – Select how users can view and access attachments. If Direct file access is enabled, users will be able to open attachments by clicking them and selecting Open.
Offline access – Specify how and when users can enable offline access to their email. Offline access copies information from users’ accounts to their device, which lets them use Outlook on the web when they’re not connected to a network. It has three options to choose – Always, Private Computer and Never.
The new Microsoft 365 admin center role assignments categorized under Azure AD into 71 administrator roles. Of them 8 roles are commonly used role assignments. They are given below with descriptions.
- Exchange Administrator – Full access to Exchange Online, create and manage groups, manage service requests, and monitor service health
- Global Administrator – Has unlimited access to all management features and most data in all admin centers
- Global Reader – Can view all administrative features and settings in all admin centers
- Helpdesk Administrator – Reset passwords and re-authenticates for all non-admins and some admin roles, manages service requests and monitors service health
- Service Support Administrator – Creates service request for Azure, Microsoft 365 and Microsoft 365 services, and monitors service health
- Sharepoint Administrator – Full access to Sharepoint Online,manages Microsoft 365 groups, manages service requests, and monitors service health
- Teams Administrator – Full access to Team and Skype admin center,manges Microsoft 365 groups and service requests, and monitor service health
- User Administrator – Reset user passwords, creates and manages users and groups, including filters, manage service requests and monitor service health
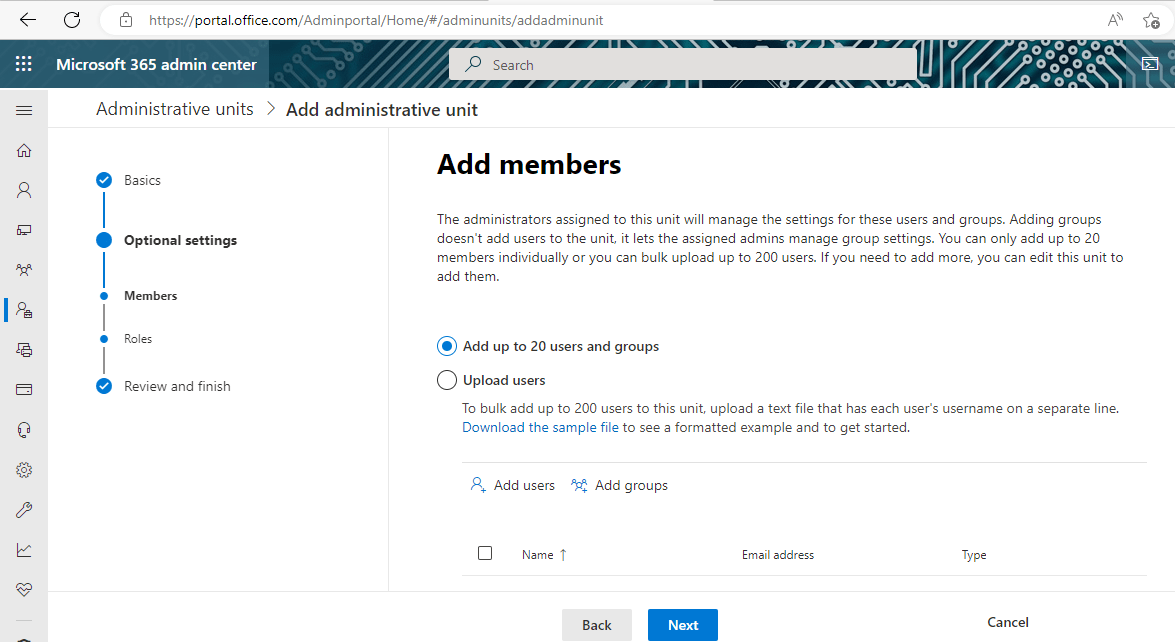
Administrative Units
An administrative unit is an Azure AD resource that can be a container for other Azure AD resources. An administrative unit can contain only users, groups, or devices.Administrative units restrict permissions in a role to any portion of your organization that you define.It can be useful to restrict administrative scope by using administrative units in organizations that are made up of independent divisions of any kind.
You can use administrative units to logically group Azure AD resources. An organization whose IT department is scattered globally might create administrative units that define relevant geographical boundaries. In another scenario, where a global organization has sub organizations that are semi-autonomous in their operations, administrative units could represent the sub organizations. Below screenshot shows how to create an administrative unit & assign members & roles on it.
Conclusion
For any Exchange & Microsoft 365 administrator, here are the top five important tips to know about permissions on Microsoft Exchange:
- Understanding role-based access control
- Managing role groups in Microsoft 365
- Configuring Role assignment policies in Exchange Online,
- Understanding Administrative units and
- Learning more about the permissions required to manage Exchange Online features and services
Thus with the extent of knowledge and learning one can do the above processes easily.
Unveil the Ultimate M365 Backup Marvel!
Empower your critical data with secure and seamless M365 backup, ensuring a fortress of protection. Unlock the full potential of your cloud infrastructure, preserving your invaluable information with unwavering confidence. This thrilling journey awaits — explore limitless possibilities of safeguarding your M365 data with a free trial today!
But that’s not all — brace yourself for an impressive feat of Exchange backup prowess! Safeguard your Microsoft Exchange Server with BDRSuite, and experience unrivaled data protection. The power to secure your vital communication hub is at your fingertips. Discover more about our Exchange backup solution!
Ready to embark on this adventure? Download BDRSuite now and take the first stride towards safeguarding your M365 environment. Embrace tranquility and immerse yourself in the realm of unparalleled M365 and Exchange backup excellence!
Related Posts
Microsoft 365 for Beginners – What is Microsoft Admin Center – Part 23
Microsoft 365 for Beginners – What is Exchange Online – Part 4
How to Backup and Restore Archive Mailbox in Exchange Server
Protecting Microsoft Exchange Online using Exchange Online Protection
Follow our Twitter and Facebook feeds for new releases, updates, insightful posts and more.

